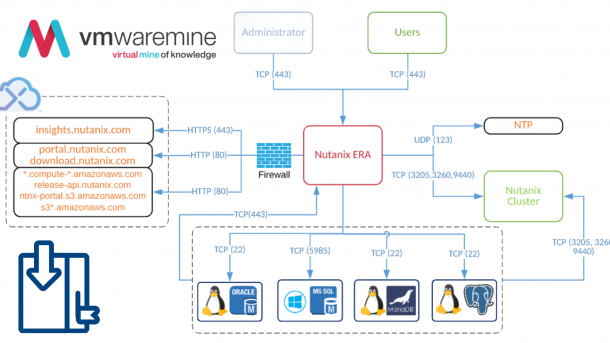
HomeLab network topology:
- LAN01 – isolated network (behind firewall) – 192.168.137.X/24 – LAN interface on firewall
- GW01 – open network – 192.168.1.X/24 – WAN interface (it is my home network)
- 192.168.137.100 – firewall IP in LAN network
- 192.168.1.100 – firewall IP in WAN network
- 192.168.137.10 – vCenter server
After PFSense homelab firewall – Part1 and PFSense homelab firewall – Part2
Is a time to do some basic configuration,
In a first instance add route into workstation which you are working from to reach network behind firewall\router. Below example how to add route on Linux system.
artur@laptop01:~$ sudo route Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface default o2.box 0.0.0.0 UG 0 0 0 wlan0 link-local * 255.255.0.0 U 1000 0 0 wlan0 192.168.1.0 * 255.255.255.0 U 2 0 0 wlan0 artur@laptop01:~$ sudo route add -net 192.168.137.0 netmask 255.255.255.0 gw 192.168.1.100 dev wlan0 artur@laptop01:~$ sudo route Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface default o2.box 0.0.0.0 UG 0 0 0 wlan0 link-local * 255.255.0.0 U 1000 0 0 wlan0 192.168.1.0 * 255.255.255.0 U 2 0 0 wlan0 192.168.137.0 192.168.1.100 255.255.255.0 UG 0 0 0 wlan0 artur@laptop01:~$
Add alias to firewall
Aliases makes easier to mange firewall rules.
- Go to Firewall – Alias – Add alias
Remove FW rule which blocks private networks.
By default on pfSense has rule on firewall which blocks all traffic from private IP addresses which comes from WAN interface. In my configuration WAN interface is not exposed to internet and all traffic are from local networks. Go to Interface –> WAN and uncheck Block private networks.
Add FW rule to pass by all traffic from WAN to LAN
- Go to Firewall – Rules -WAN tab – Add rule button
- Save and apply changes
artur@laptop01:~$ ping 192.168.137.200 PING 192.168.137.200 (192.168.137.200) 56(84) bytes of data. 64 bytes from 192.168.137.200: icmp_req=92 ttl=127 time=5.31 ms 64 bytes from 192.168.137.200: icmp_req=93 ttl=127 time=3.67 ms 64 bytes from 192.168.137.200: icmp_req=94 ttl=127 time=3.84 ms 64 bytes from 192.168.137.200: icmp_req=95 ttl=127 time=1.84 ms ^C --- 192.168.137.200 ping statistics --- 95 packets transmitted, 4 received, 95% packet loss, time 94734ms
If it works, remove ANY-ANY rule and create custom rule, for example, RDP service to vCenter server
- Go to Firewall – Rules -WAN tab – Add rule button
- provide necessary information
- save and apply configuration