Second part of my Single Sign On series is about authentication to vSphere with and without Single Sign On. The default vCenter Single Sign-On administrator user ID is admin@System-Domain – it cannot be change and password was set during Single Sign On installation process. make sure you remember SSO admin password because you will need it for various installation and administration tasks. You can create Single Sign-On administrator users with the Single Sign-On administration tool in the vSphere Web Client.
[box type=”warning”] Notice: admin@system-domain user is a Single Sign On user with Administrative rights ONLY to Single Sign On server and has not right in vCenter server.[/box]
How the authentication works:
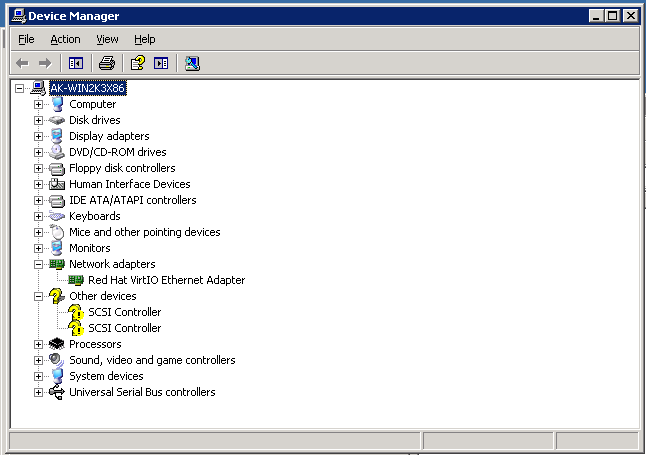
Pre-vSphere 5.1
In version pre vCenter Server 5.1, when a user connects to vCenter Server, vCenter Server authenticates the user by validating the user credentials against an Active Directory domain or the list of local operating system users.
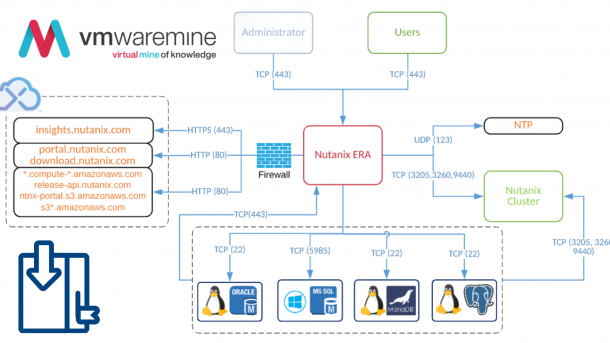
When user log in to vCenter server the authentication request is sent in fact to STS – Security Token Service (which is SSO secure interface), STS checks user credential against Active Directory (you can have more than one AD domain attached to SSO server) openLDAP, local OS users. Upon successful, STS generated SAML 2.0 token, it is used for authentication to vCenter server.
Directory services such as Active Directory or openLDAP are not mandatory, Single Sign On service has it’s own database to store users and credentials. It is pretty useful in use case when you don’t have any directory services or SSO and vCenter server is located in security zone without access to central directory services.